You didn’t buy OneTrust because you wanted more work. You bought it to solve a problem: manage DSARs, stay compliant, reduce risk. And for a while, maybe it did.
But somewhere along the way, the tool that was supposed to simplify privacy started creating more trouble than it solved. You’re babysitting workflows instead of advancing your program. Engineering is fielding tickets for every deletion request. Your data map is really just a spreadsheet that’s always three months stale. And you only find new systems when there’s an audit.
If this sounds familiar, you’re not alone. Hundreds of privacy teams have been right where you are, and decided to make a switch to DataGrail.
Here’s how to build a business case that actually gets approved.
Lead with risk, not features
The most common mistake privacy leaders make when pitching a platform switch is leading with capability comparisons. DataGrail is faster. DataGrail is more automated. DataGrail has better reviews. All true. But none of it moves budget.
What moves budget is risk. Specifically, quantifiable business risk that executives can see, feel, and fear.
Try this exercise with us: Go to your own website right now. Try to opt out of having your personal information sold. Can you do it? Does the button actually work? Now refresh the page. Are tracking pixels still firing?
Tip: Confirm if your website honors opt-outs automatically with DataGrail’s free Consent Checker
If you can’t answer those questions confidently, neither can your legal team. And neither can a regulator.
This is the real argument for DataGrail: not that it’s “better,” but that your current state leaves you exposed. Demand letters. Regulatory scrutiny. Lost customers. That’s what unlocks executive attention and budget.
Quantify the hidden tax of your current tool
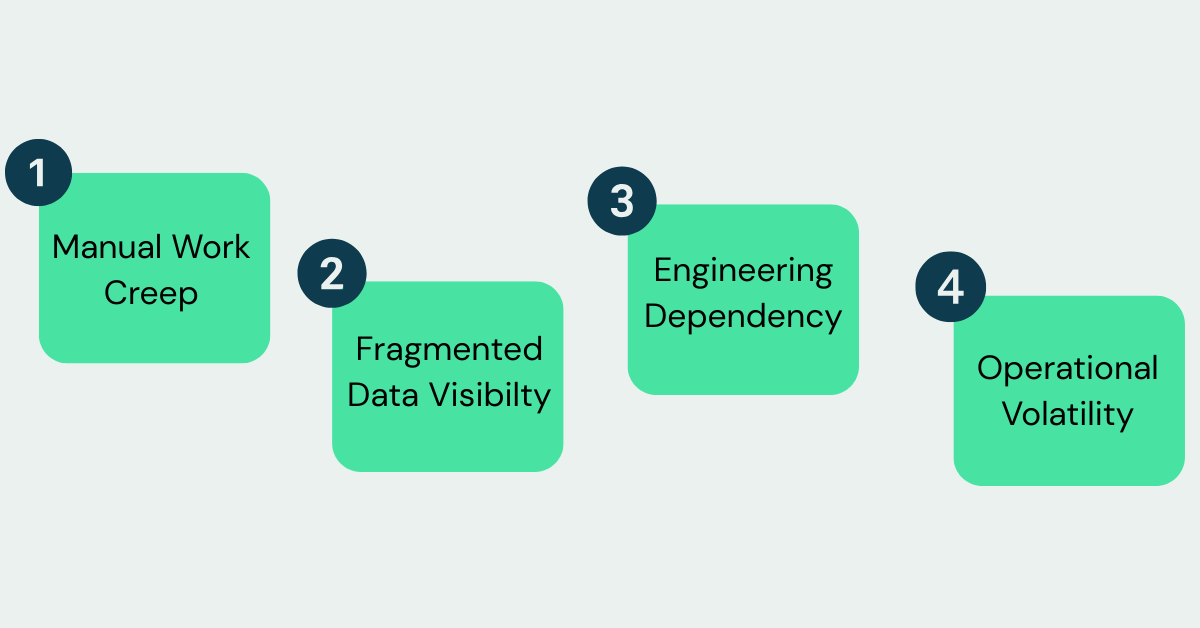
Before you can propose a solution, we recommend that you name the problem clearly. For most OneTrust users, the pain falls into one or more of the four categories below.
- Manual Work Creep. How many hours per week does your team spend reconciling DSAR data across systems? How many of those requests require engineering involvement? One company reported needing eighteen staff members, including technical roles running custom scripts. All of this increases the likelihood of human error that could lead to a regulatory fine.
- Fragmented Data Visibility. OneTrust often relies on manual system tracking. That means your data map reflects what you knew existed six months ago, not what’s actually running today. Shadow IT and new SaaS tools slip through the cracks. Third-party integrations go unmonitored. This lack of visibility makes it impossible to ensure we’re properly respecting user opt outs.
- Engineering Dependency. If your privacy team can’t fulfill a deletion request without filing a ticket, you’ve created a bottleneck that slows compliance and frustrates both teams. Allocating valuable engineers to routine deletion requests not only wastes their time, but also pushes a constant prioritization struggle that leaves compliance on the line.
- Contract Volatility. Multiple OneTrust users have reported sudden, 3-10x renewal increases, sometimes arriving days before contract expiration. This along with slow support response times that jam up planning cycles. No one wants surprise budgetary impacts and even harder to justify ROI.
If you add it all up: staffing costs, delayed SLAs, compliance exposure, brand risk. That’s your “invisible tax.” That’s the foundation of your business case to switch.
Translate operational tax into business risk
For privacy teams doing the work, the obvious value is strategic capacity: every hour spent configuring workflows or chasing engineering tickets is an hour not spent building a mature program. But, that’s just the start. In terms of business value, this translates into significant reduction in monetary risk. Let’s take a look at an example:
Example business risk exposure calculation
While being a OneTrust customer doesn’t in and of itself increase our risk, it doesn’t automatically eliminate it either. Privacy risk is directly connected to how well we configure and manage our privacy tool, and OneTrust has known technical and operational complexity that makes this process highly challenging.
Consent Enforcement & Proof Failures
Many OneTrust customers report inability to confidently confirm that consent banners work as intended, insufficient consent logs, and limited executive-grade reporting. Technical issues such as misfiring tags or unclear consent states are difficult to detect and prove.
Risk impact: Inability to verify consent enforcement increases the likelihood of consent-based enforcement or litigation by approximately 2-4x, particularly in consumer-facing businesses.
Data Subject Request (DSAR) Execution Risk
Across customer feedback, OneTrust users consistently report manual or semi-manual DSAR processing, difficulty scaling as volumes increase, and challenges proving timely and complete fulfillment.
Risk impact: Organizations handling DSARs manually at scale face an estimated 2x increase in enforcement likelihood related to access and deletion rights.
Data Map, Inventory & Accountability Gaps
Customer feedback indicates that OneTrust’s data mapping and inventory capabilities are costly, difficult to maintain, or underutilized, resulting in incomplete visibility into systems, vendors, and data flows.
Risk impact: Incomplete inventories increase the likelihood that a narrow inquiry escalates into a broader enforcement action, raising both cost and severity.
Privacy Assessments (PIA/DPIA/AI) Coverage Failures
Many OneTrust customers report difficulty keeping assessments current or scaling them as the business evolves, leading to skipped or outdated assessments.
Risk impact: Missing or outdated assessments significantly increase penalty severity and mandated remediation once regulators engage.
Bottom Line for Leadership
Continuing with OneTrust exposes the company to avoidable regulatory and litigation risk driven by known control weaknesses. If we assume a baseline risk of $1,000,000, the technical and operational gaps in our current platform increase our total risk exposure by over 9X or $9,500,000.
These numbers are illustrative. Use our no-cost Migration ROI Calculator to calculate your own potential risk exposure and generate a business case in seconds.
Address the needs of migration stakeholders
A strong business case lives or dies on internal alignment. Aside from the overall risk reduction impacts mentioned above, the following are tangible benefits for the stakeholders that typically need to approve the migration and ensure its success.
For Legal, the decision is about defensibility under pressure. When regulators ask how you operationalize deletion requests, or when a demand letter arrives and you need to prove what happened, the worst answer is “we thought OneTrust handled it.”
DataGrail is built to produce proof: verifiable consent handling, automation that reduces human error, and audit trails that stand up in scrutiny. That shift matters because it transforms privacy from a best-effort process into documented, repeatable compliance—exactly the type of recordkeeping legal teams need to reduce exposure and confidently defend the company.
For Security, DataGrail’s discovery and continuous monitoring help turn privacy risk into something that can be measured, tracked, and resolved instead of a blind spot that only shows up during audits or incidents.
Meanwhile, Engineering will support the switch if it removes pain, not adds it: DataGrail replaces the ticket-based model where every DSAR becomes an engineering task, eliminating custom scripts, recurring queues, and privacy work that quietly drains sprint capacity.
Once Legal sees defensibility, Security sees reduced risk, and Engineering sees regained bandwidth, the finance narrative becomes straightforward: inaction is expensive, prevention is cheaper, and DataGrail delivers ROI by lowering exposure while materially reducing the internal cost of running privacy. Get these three aligned and the CFO conversation becomes a formality.
Position DataGrail as operational compression
Once you’ve established the cost of the status quo, the next step is showing how DataGrail directly addresses each of the pain points above.
On automation: DataGrail’s DSAR handling consistently outperforms legacy tools. One company reduced fulfillment time to fifteen minutes per request, handled by a single team member just after migrating. That’s not incremental improvement; that’s a category shift.
On data discovery: DataGrail continuously identifies systems holding personal data, including third-party tools that manual processes miss. You’ll know where your risk actually lives before an auditor asks.
On engineering lift: With over 2,400 integrations and automated workflows, DataGrail removes the ticket-based model that creates friction between privacy and engineering teams.
On support: Users consistently rate DataGrail’s support quality significantly higher than OneTrust’s. That matters when you’re mid-migration or troubleshooting a consent issue at quarter-end.
Neutralize the migration objection
The most common pushback you’ll hear is some version of “we just don’t want to go through another implementation.”
That’s fair. Re-implementation fatigue is real. But the comparison isn’t between OneTrust and a painful migration that delivers the same results again. Instead, it’s between the ongoing cost of staying and the one-time cost of switching.
DataGrail’s implementation is designed to be faster and lighter than what you experienced with OneTrust. Automated system detection replaces manual module configuration. Streamlined onboarding replaces months of setup. And DataGrail’s success team takes point on technical orchestration, so your team isn’t rebuilding from scratch.
The question isn’t “is migration painful?” The question is “is it more painful than another year of manual overhead, stale data maps, and compliance exposure?”
Close with the executive summary
When you walk into the room, here’s your one-liner:
“OneTrust costs more, risks more, and scales worse. DataGrail cuts the overhead, closes the gaps, and gives us our time back so we can finally run a privacy program instead of maintaining a platform.”
Back it up with concrete numbers: use our OneTrust Migration ROI calculator to show exactly how much OneTrust is costing you in risk exposure today and the financial difference DataGrail can make.
Privacy programs don’t get budget because they’re efficient. They get buy-in when business risk can be quantified and managed. You’ve now got that covered.