AI-Powered Privacy Assessments
Create fast, accurate privacy assessments with Vera—your integrated AI agent.
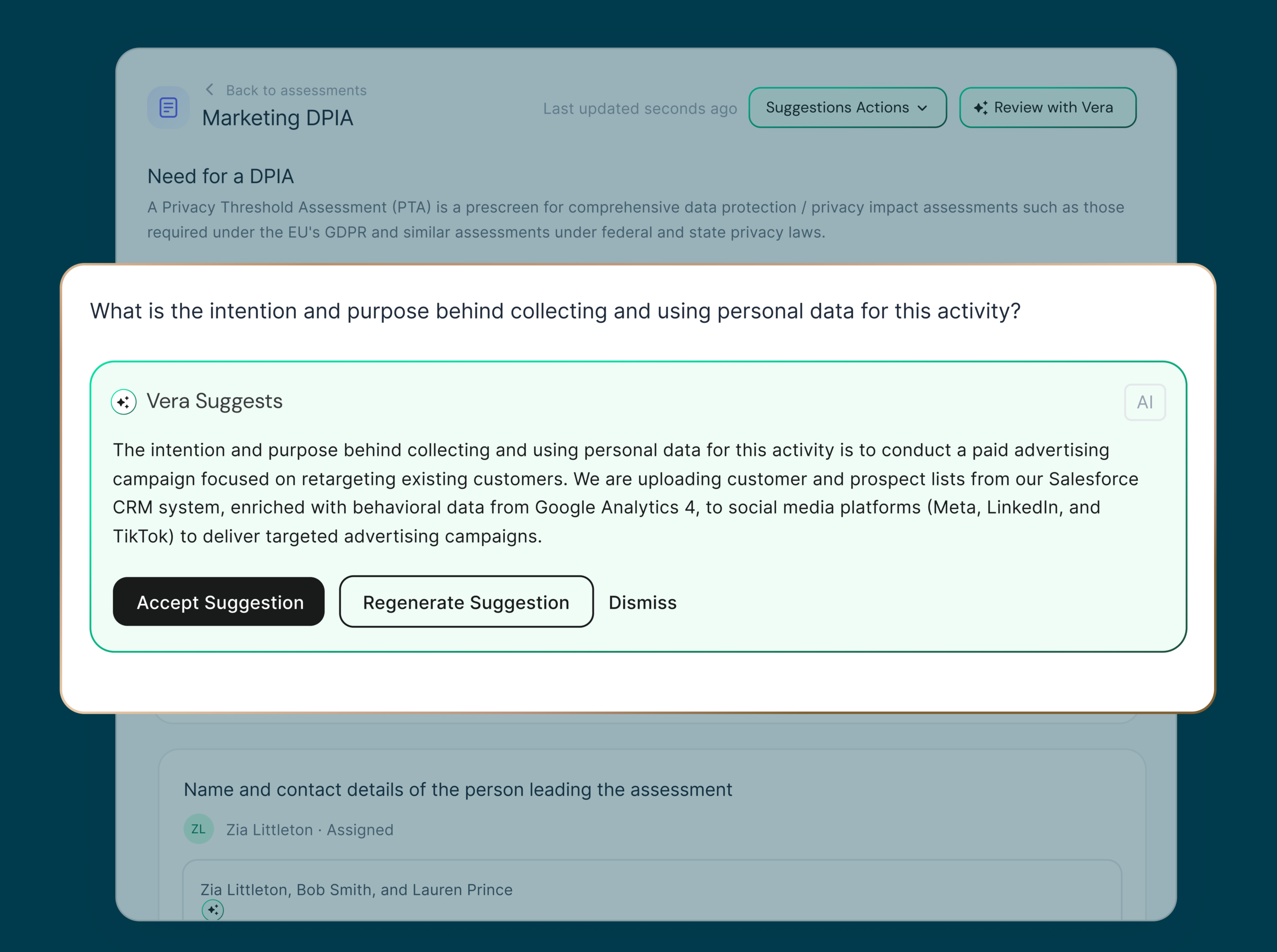
Let AI do the heavy lifting
Vera uses your real privacy program and business context to draft assessment responses in minutes.
- Supports PIAs, DPIAs, TIAs, AI risk assessments
- Provides reasoning and citations for every suggestion
- Completed assessments are saved and reusable
Get better answers with global context
Assessments AutoFill is powered by the same privacy knowledge graph underpinning the DataGrail platform.
- Bi-directional enrichment from Live Data Map
- New suggestions automatically reflect program changes
- Track uncovered risks directly in Risk Register
Streamline reviews and approvals
Never email out a 10-page PDF again. DataGrail gives stakeholders a central place to review what matters and more forward—fast.
- Contributors can review without a DataGrail account
- Flag responses for human review
- Formal risk acceptance workflows close the audit gap

Track risks and ensure compliance
Easily flag risks during the review process and send them to Risk Register for tracking and resolution.
- Human and AI risk detection
- AI-generated prioritization and action plans
- Global risk tracking and collaboration
- Version tracking and audit trails for CalPrivacy
Built on the DataGrail Platform
DataGrail delivers integrated AI for resource-strapped privacy teams who need to scale with confidence.
No engineering degree required
Replace manual workflows and bottlenecks with a full suite of intuitive privacy automation products and 2,500+ integrations designed for non-technical teams.
Always-on privacy visibility
Go from surveys and spreadsheets to a Live AI-powered Data Map that powers better RoPAs, evidence-based assessments and always-on risk detection.
Privacy partner from day 1 to 1001
Your named human expert is dedicated to your success in onboarding, regulation readiness, and achieving ongoing program goals across your entire journey.
No-compromise security promise
DataGrail is the only platform engineered from the ground up for agentic privacy work in production. Single tenant. No training on your data. Six-stage prompt protection.
Frequently Asked Questions
What types of assessments does DataGrail support?
DataGrail supports PIAs, DPIAs, AI risk assessments, Transfer Impact Assessments (TIAs), vendor assessments, and custom templates. Vera can auto-populate all of them using your live privacy program data and documentation.
Does my team need engineering resources to use this?
No. DataGrail’s assessments are purpose-built for non-technical privacy managers. You can deploy, customize, and update assessment workflows without writing code or filing an engineering ticket.
How does Vera source the answers it suggests?
Vera draws from multiple sources simultaneously: your live DataGrail data map, uploaded documentation (PRDs, DPAs, policies), previously completed assessments, and a knowledge base covering 12,000+ applications and global regulatory requirements. Every suggested answer cites its source for confident human review.
Is my assessment data used to train Vera or any AI models?
Never. DataGrail operates a single-tenant architecture and Vera is built on a zero-training data policy. Your sensitive privacy program data is never used to train AI models.
How do assessments connect to the rest of the DataGrail platform?
Assessment findings feed directly into the Risk Register, RoPAs, and the Live Data Map — bidirectionally. New risks discovered during an assessment automatically surface in your centralized risk hub, and system changes can trigger re-assessments without any manual monitoring.
What happens when a regulation changes?
Vera maintains a continuously updated regulatory knowledge base. When new requirements affect your assessments, Vera surfaces the impact in context so your team can adapt quickly. Your DataGrail privacy expert is also on hand for strategic guidance.

Let’s get started
Ready to level up your privacy program?
We're here to help.








